vmmap
Command vmmap
vmmap displays the target process's entire memory space mapping.
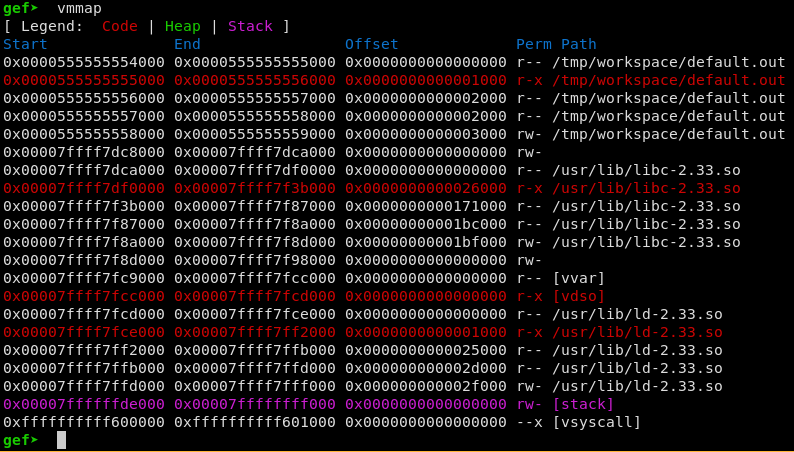
Interestingly, it helps finding secret gems: as an aware reader might have seen, memory mapping
differs from one architecture to another (this is one of the main reasons I started GEF in a first
place). For example, you can learn that ELF running on SPARC architectures always have their .data
and heap sections set as Read/Write/Execute.
vmmap can accept multiple arguments, either patterns to match again mapping names, or addresses
to determine which section it belongs to:
-a/--addr:- filter by address -> parses the next argument as an integer or asks gdb to interpret the value
-n/--name:- filter based on section name
- If nothing is specified, it prints a warning and guesses the type
The address can be also be given in the form of a register or variable.
And you can do all of them in one command 🙂